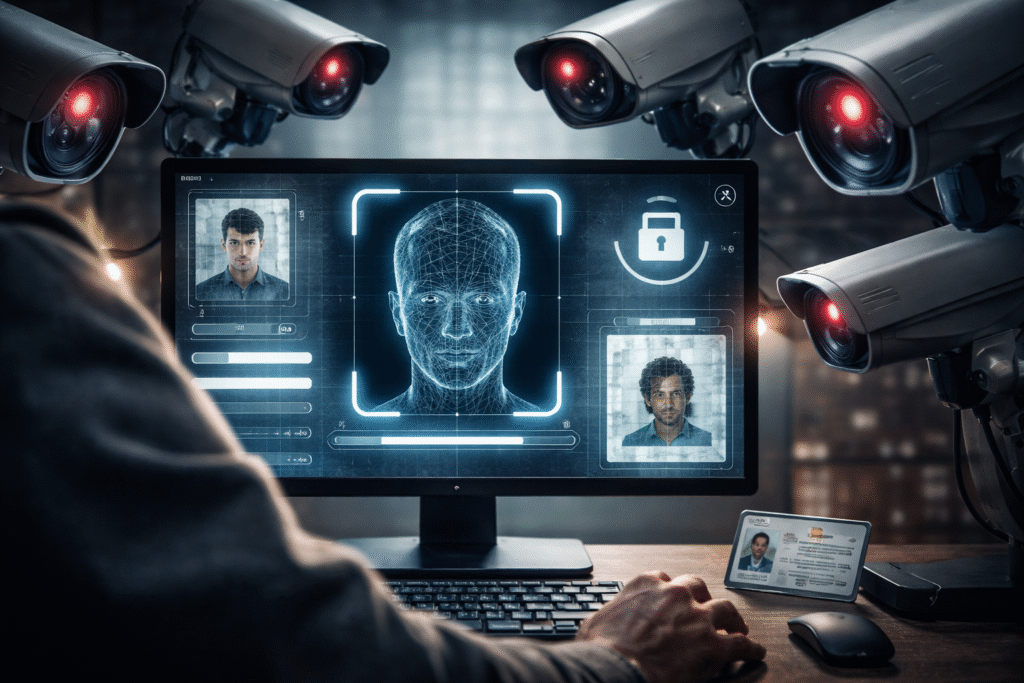
Pegasus spyware can secretly turn smartphones into surveillance tools. Experts explain how infections happen and how users can check their devices for signs of compromise.
Posts published in “Mass Surveillance”
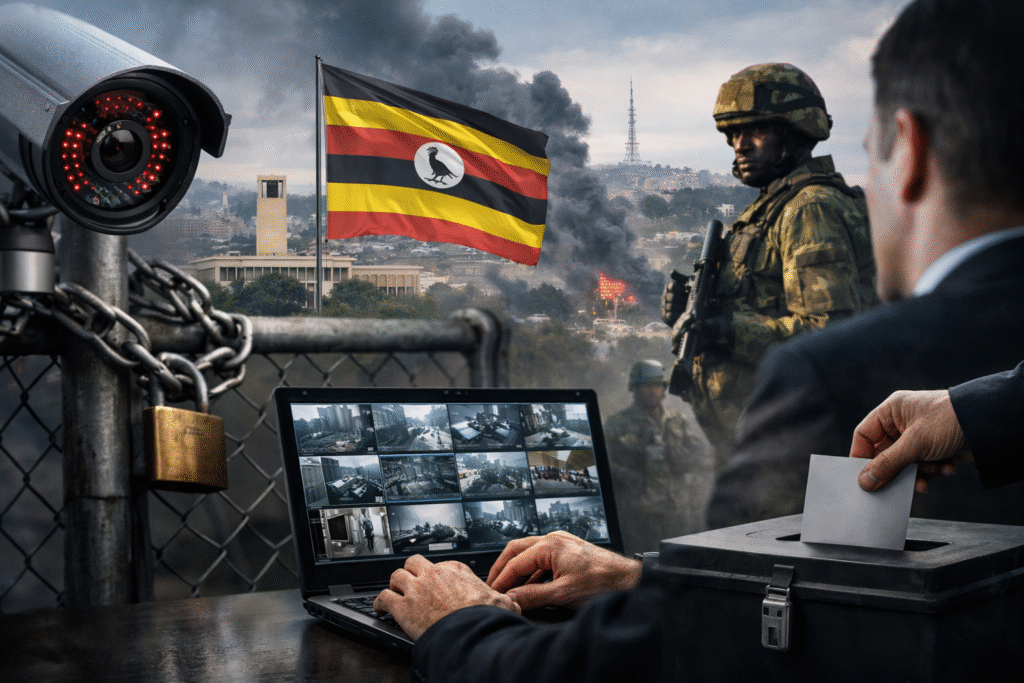
U.S. senators including Lindsey Graham, James Lankford, and Jacky Rosen pushed for funding tools to help Iranians bypass censorship and access VPNs. Critics note these same lawmakers have supported surveillance and encryption backdoor policies at home.
Lawmakers initially demanded mandatory body cameras on ICE to increase accountability after high-profile enforcement controversies. Now some Democratic leaders are expressing worry the cameras could be misused for mass surveillance.
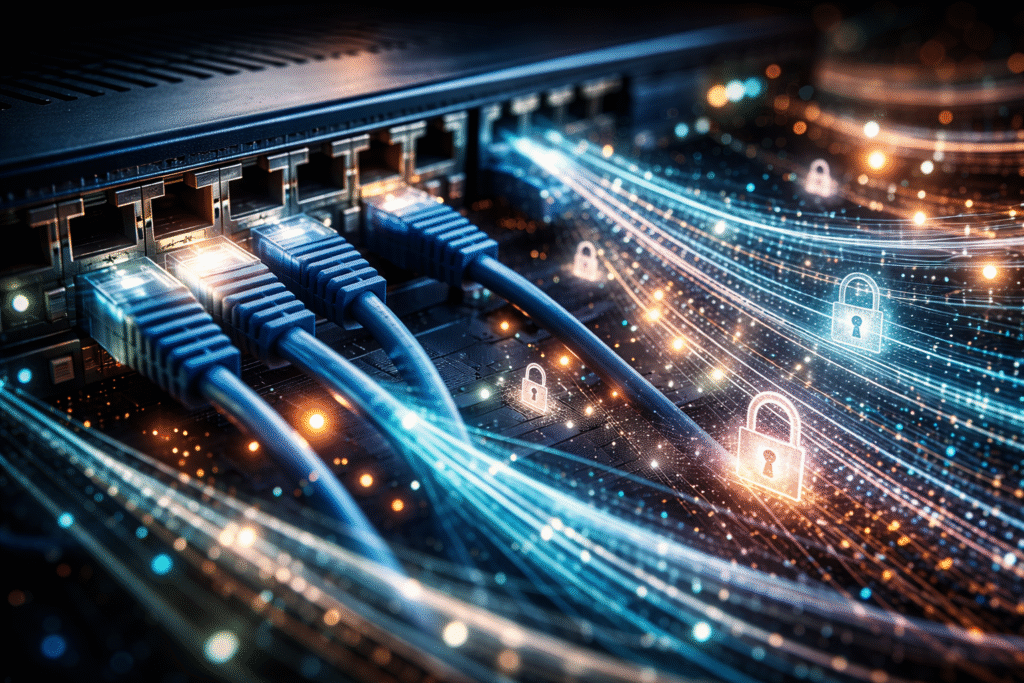
A global coalition of regulators is quietly turning the open web into a gated community where every login begins with an ID check. By Cam…
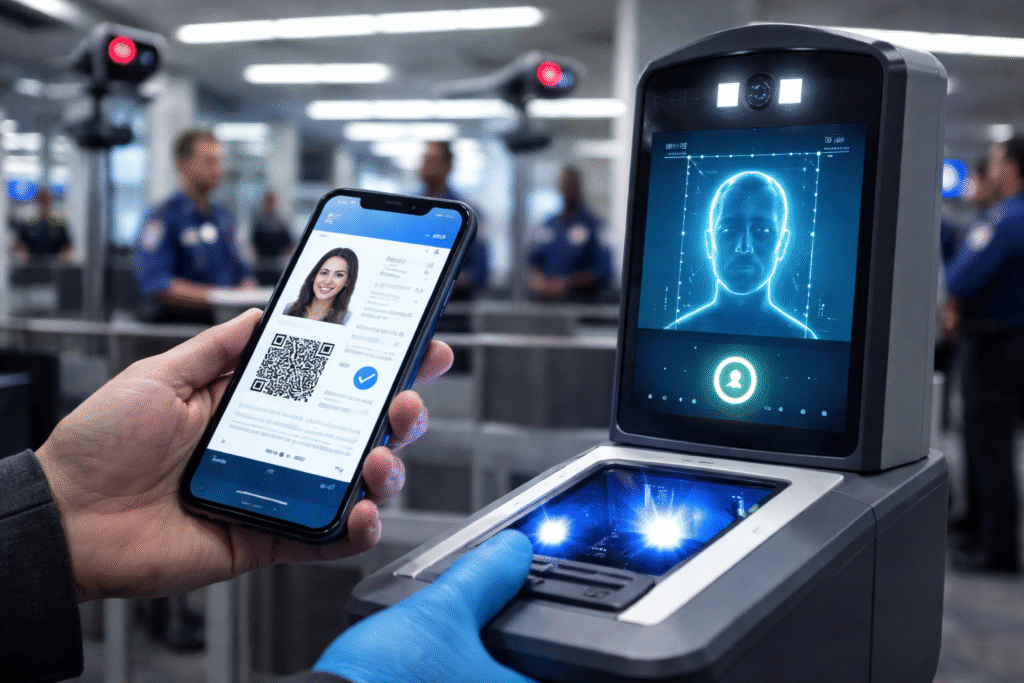
TSA’s new digital ID plan transforms airport screening into a data exchange, where every shortcut comes with a deeper surrender of personal detail. By Ken…
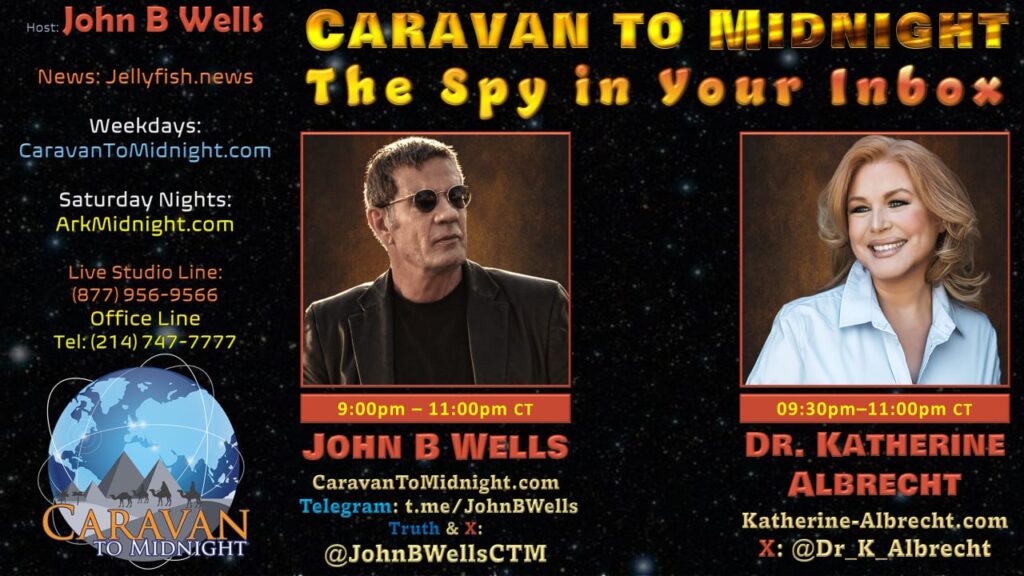
Most people still believe email is private as long as no human is reading it. That assumption is no longer true. Today, artificial intelligence reads, analyzes, remembers, and profiles your communications in real time — building behavioral maps, predicting intent, and quietly turning personal correspondence into usable intelligence.
By SIMINA MISTREANU It is a soulful folk song, filled with feeling and history: A love-stricken young man tells God about his hopes and dreams of…
By disguising coercion as consent, the EU’s plan enlists tech companies as willing agents in its quiet expansion of digital surveillance. By Ken Macon European…
Russia is also currently rolling out biometric ID verification terminals at businesses courtesy of a Russian super bank. By The WinePress Russia is becoming the…
By Sundance Following the midterm “shellacking” of 2010, President Obama and Eric Holder began the “secret research project” targeting political opposition using the IRS. DOJ…