- revision of this page (50.1 MB) | The Deep State Shadow Government (Drain the Swamp)
- HTML version of Michael T. McKibben AFI backgrounder
- HTML version of Tampere, A. (Oct. 14, 2013). Michael McKibben: Facebook is built on technology stolen from us. Estonia Today (EstiPäevaleht).
- Breyer/Accel/Zuckerberg Oct. 26, 2005 Stanford Solicitation/Conversion, Transcript | YouTube | Raw *.mp4 file (165 MB)
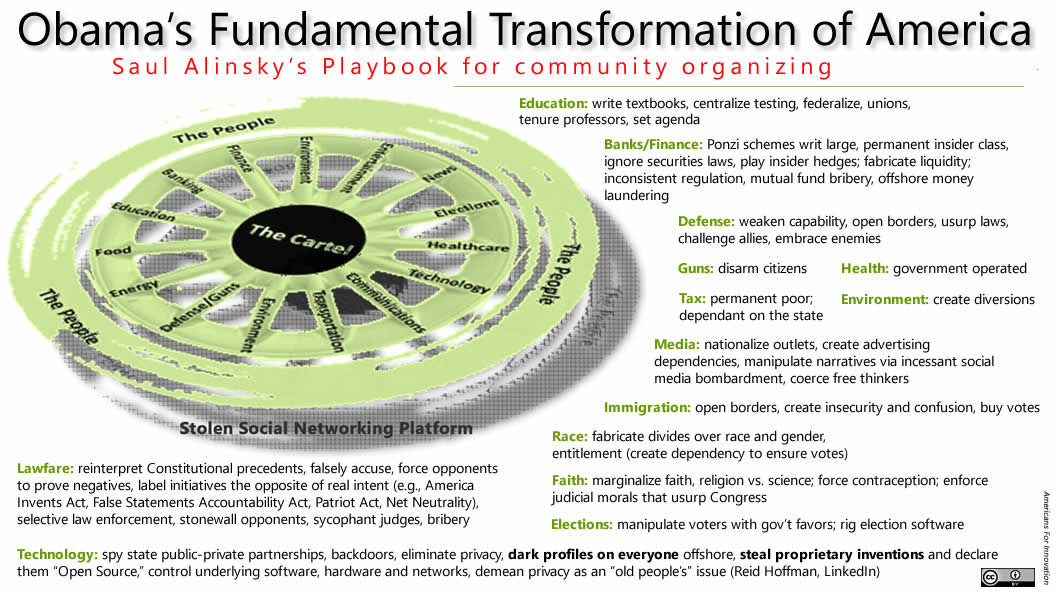
Compiled by Americans for Innovation Investigators, Latest rev. Dec. 23, 2020 https://tinyurl.com/y8ul6zj9
Please be patient! If this is your first time to access this timeline or if it has been updated since your last visit, it contains many graphics and photos that must load to your browser. Once downloaded the first time (into your Internet browser’s temporary cache files), the site will load more quickly after that. New evidence is added almost daily.
Findings of Fact, Timeline & Database
hijacking the Internet
The following 1990-2018 timeline and supporting facts provide unmistakable evidence of dereliction of duty, fraud, public corruption, the appearance of impropriety, racketeering, monopoly and anti-trust by senior United States government officials, Harvard, Yale and Stanford academics and alumni, judges, law firms and their commercial accomplices. American patent law itself has been hijacked by these individuals and their organizations.
Alternatively, go to an interactive database library for a list and links to all the files, listed by date and alphabetically, at https://www.fbcoverup.com/docs/library/
The American economic engine is being dismantled by deep-pocket intellectual property thieves. They have made the U.S. Patent Office their private toy box.
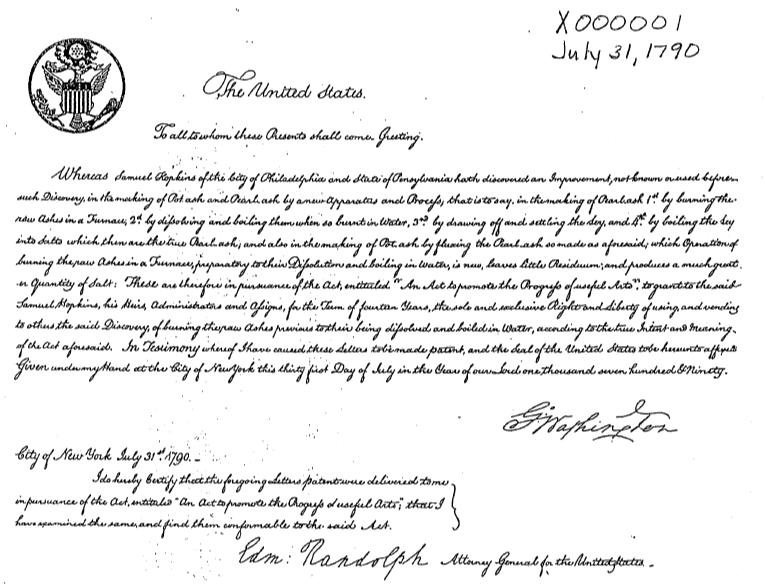
Constitutional quiz: What are the -only property rights that the Founders considered important enough to actually write into the Constitution?
Answer: patents and copyrights. (U.S. Constitution, Article I, Section 8, Clause 8.) President George Washington himself signed the first patent, U.S. Patent No. X0000001, on July 31, 1790.
The Founders knew the importance of innovation and invention and created the patent system to protect the young republic’s inventors. They believed patents would grow the economy with new ideas that create new jobs and wealth. But without patent protection, inventors and their investors have no incentive to risk their time and treasure to do the hard work of inventing.
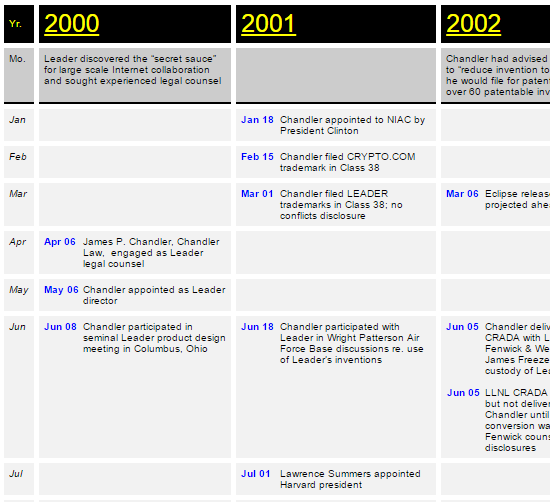
Leader Technologies of Columbus, Ohio, risked 145,000 man-hours over five years with an investment of over $10 million to invent the platform that enables social networking. Leader legally filed for patents that they believed would protect their invention.
But a pattern of public-private corruption—as shown in the following timeline—allowed the well-financed vendor of social networking to steal Leader’s invention, reproduce the design, and then use their ill-gotten gains to perpetuate their crime. They excused their theft by falsely asserting that the technology system was “open source” (i.e., “free”) software.
What inventor wants to spend years perfecting and patenting an invention that may then be stolen with impunity? What investor will trust his investment to a government that will not protect the entrepreneurial risk?
When inventors are not rewarded for their inventions, society suffers. China, once known for inventions like paper and fireworks, is now notorious for industrial espionage and intellectual property theft and for copying rather than innovating.
Do we want to risk becoming another China?
To foster the inventive spirit that made America the world’s innovator, we must protect and reward our inventors, and address the corruption that has allowed companies like Leader Technologies, the true inventors of social networking, to be fleeced by the system that was supposed to protect them.
Theft of the social networking invention
Brief summary of the MANY smoking guns in this collusion:
| Oct. 11, 1996 | False Statements Accountability Act—parties can lie to Congress and courts); |
| Nov. 29, 2001 | IBM forms The Eclipse Foundation |
| Jun. 05, 2002 | Chandler takes custody of Leader’s invention source code |
| Aug. 29, 2002 | Leader’s invention appears in Eclipse version 2.0.1 |
| Aug. 30, 2002 | Chandler’s notes confirm IBM conspiracy to misappropriate Leader’s invention |
| Feb. 2-5, 2004 | IBM EclipseCon 2004, Facebook goes live |
| Apr. 12, 2004 | Anne-Marie Slaughter proposed A New World Order |
| Dec. 08, 2004 | IBM”unable to locate” originator of Eclipse code—Leader Technologies |
| Sep. 02, 2008 | A New World Order to “Fundamentally transform America” |
| Sep. 09, 2008 | Eclipse boasts 191 members); Dec. 12, 2008 (FISA court gives Eric Holder dictatorial powers |
| Jun. 06, 2009 | Facebook starts feeding user data to the NSA illegally |
| Jul. 09, 2009 | Sidney Blumenthal writes Facebook into Hillary CFR speech |
| Aug. 03, 2009 | Fenwick & West LLP disclosed Leader as prior art on Andreessen social patents, but not on Zuckerberg patents they filed |
| Apr. 2010 | Zuckerberg refused to provide discovery in Leader v. Facebook |
| Jun. 24, 2010 | Leonard P. Stark shoehorned into Leader v. Facebook 30 days before trial; and Larry Summers’ chief of staff, Marne L. Levine went to work for Facebook on the same day |
| Aug. 10, 2010 | Leonard P. Stark confirmed as judge, just two weeks after the Leader v. Facebook trial |
| Feb. 17, 2011 | Obama dines and toasts with Eclipse members in Silicon Valley |
| Jun. 26, 2012 | State Department promoted Facebook use during public litigation that proved Facebook infringes Leader Technologies’ patent on 11 of 11 claims and no prior art |
| Jul. 18, 2012 | 28 Zuckerberg hard drives re-discovered! |
| Jun. 06, 2013 | Edward Snowden exposed illegal NSA activity |
| Feb. 08, 2015 | HSBC whistleblower Hervé Falciani exposed Facebook underwriter Deep State |
| Mar. 02, 2015 | Obama met with Technology CEO Council at White House – All “IBM / NSA The Internet of Things” Deep State members |
| Oct. 10, 2015 | Obama made mystery trip to Qualcomm |
| Oct. 12, 2015 | Dell bought EMC – Both Deep State members |
| Dec. 01, 2015 | Zuckerberg announces $45 billion of fraudulent conveyances |
The summary above is not exhaustive, but merely representative of the massive fraud and racketeering that has occurred and continues to occur.
This is the story and timeline of the theft of the invention called “social networking.” The thieves are a group we call the “Cartel.” and “Deep State.” Their motives are ancient. They yearn for money and power. Their goal is a “New World Order.” Theft of Columbus, Ohio innovator Leader Technologies’ invention enabled them to unify their communications, monitor and control “the masses,” and fulfill their rapacious grab for your assets and your liberty.
The U.S. court-proven facts are that Columbus, Ohio innovator, Michael McKibben, and the company he founded, Leader Technologies, invented social networking in the late 1990’s. Prior to that, McKibben had re-built AT&T’s email system in record time for release with Microsoft’s much ballyhooed Windows 95.
In 6, Leader was awarded its first patent. However, once the Deep State learned about Leader’s invention from an unscrupulous patent attorney and adviser to IBM and the NSA, they wanted it so badly they broke many laws to get it. The invention enabled them to create “The Internet of Things” or “The Internet of Everything” where they could permanently control the digital economy in all its aspects: communications, banking, law, energy, finance, elections, defense, technology, communications, media, healthcare, education, entertainment, politics, guns, food, environment and news.
This sounds like Hollywood fiction, but as you will read in these pages, it is all too real.
The roots of the modern day “One World Order” agenda go back to the 1700’s and philosopher Emmanuel Kant’s essay. In the 20th century, President Woodrow Wilson’s failed effort to form The League of Nations eventually became The United Nations. The disciples of this soulless, mechanistic agenda include George Soros, Bilderberg Group, the 1910 Jekyll Island Club duck-hunt, World Economic Forum (Davos), Council on Foreign Relations, Wall Street, Silicon Valley, and a slew of politicians, judges and bureaucrats. They benefit personally through investment gains and insider information.
World government is the notion of a common political authority for all of humanity, yielding a global government and a single state. Such a government could come into existence either through violent and compulsory world domination or through peaceful and voluntary supranational union. In such a world, national constitutions must be subservient to the single state.
Proponents of A New World Order are betting against America
On Jan. 05, 2011, new world order godfather and post-WWII Hungarian immigrant to America, George Soros (György Schwartz), stated that the “new world order” will be a healthy, if painful [violent] adjustment.” He continued, “China will be the ‘engine driving it forward and the U.S. will be actually a drag that is being pulled along through a gradual decline in the dollar.'”[294]
Education or Propaganda? The minds of our youth are targeted
Nowhere is more telling of the Deep State’s agenda than the uproar over Common Core. Critical to the Deep State agenda is the centralized control of education via Common Core in secondary education and M.O.O.C. (Massive Open Online Course) in higher education. Just like the re-education camps of every totalitarian ideology before them (like Mao, Lenin, Pol Pot, Stalin, Hitler, Brownshirts, Komsomol), the Deep State works to control the “narratives” that our children learn.
Where the facts do not fit the Deep State narrative, the facts are ignored or altered. They want to grow obedient, docile, faithless worker bees for their factories. Just like George Orwell envisioned in 1984, gone will be free thinking, free will and individuality. Liberty will be replaced by oligarchies, a permanent under-class, doublespeak, political correctness, disrespect, reading between the lines, hate, intolerance, inequality and brutality.
The digital part of this remaking of education is well down the path. Most secondary schools use Google Docs almost exclusively for their document sharing. In universities, M.O.O.C. curricula are rapidly replacing individualized instruction in favor of the allegedly more “rich” (cleansed and censored) content of “Big Data” and “The Cloud.”
Universities are being connected using The Ohio State University’s IBM / Microsoft / Oracle / SAP / Eclipse data center as an international M.O.O.C. network hub that Presidential candidate John Kasich approved. The supply of Deep State shiny things to lure educators, parents and students into this morally dark world appears unstoppable as the “users” mainline on the digital drugs.
This Leader v. Facebook timeline (below) reveals Deep State names, places and illegal acts
Hillary Clinton’s political adviser, Anne-Marie Slaughter (2009-2013) implemented her book—A New World Order (Princeton Press 2004)—when she worked for Hillary at the State Department. She started promoting Facebook at the State Department in 2009, even though Facebook did not have the intellectual property rights. Of note, Slaughter has Hungarian immigrant connections by marriage with Soros, Intel’s Andy Grove and IDG-Accel Partners (China)’s John P. Breyer. Accel is Facebook’s 2nd largest shareholder.
Bookmark: #saul-alinskyLying is a Saul D. Alinsky tactic (and also permitted in the Koran when Muslims are dealing with Westerners, Christians and Jews—Qur’an 3:28)
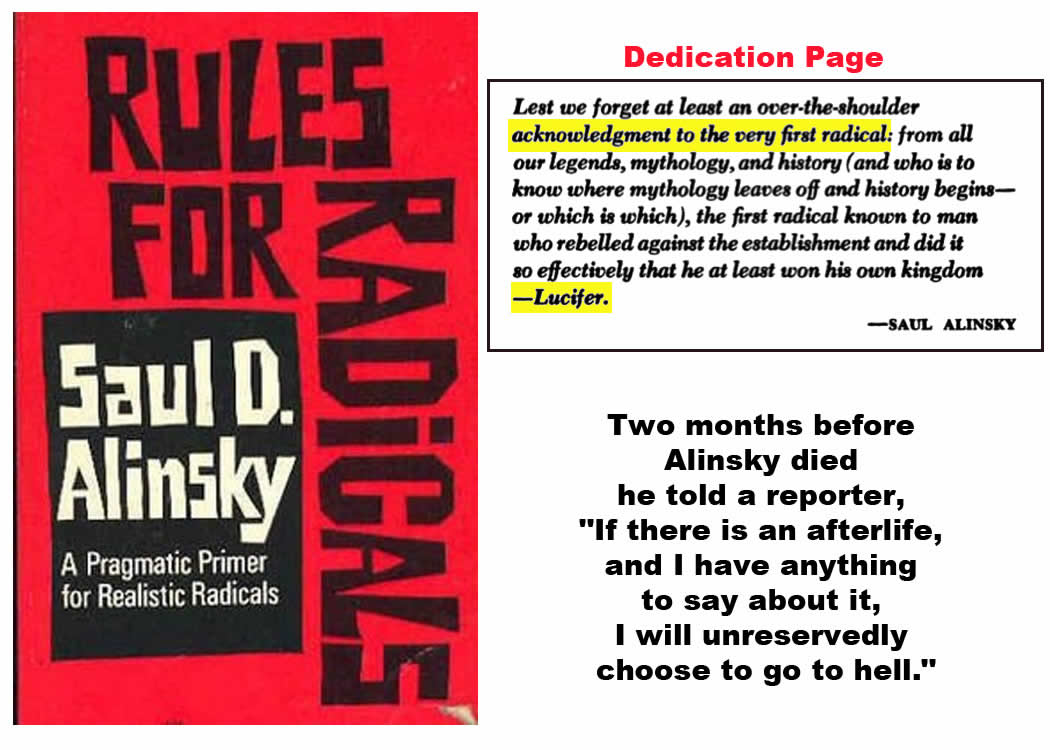
To gain control of the world’s information (and thus its money and power), the Deep State employs the political organizing tactics of Saul D. Alinsky. Hillary Clinton is an expert. She wrote her undergraduate thesis on Alinsky and corresponded with him.[299] Barack Obama employs Alinsky’s bible—12 Rules for Radicals (Random House 1971).
Tellingly, Alinsky dedicated 12 Rules to Lucifer, who he calls the original radical. Lucifer is one of the names for Satan, the Devil, the Evil One and The Dragon (The Book of Revelations 12: 2; 20:2).
The Obamas and Clintons employ Alinksy’s habitual lying technique: Keep the enemy confused and on its heels working to keep up with your lies. Lies also often become truths if repeated incessantly. For example, the lies about Zuckerberg and Facebook in The Social Network movie are accepted as the truth by many.
In the movie and in sworn testimony, Zuckerberg claimed to have invented Facebook in a few weeks, while preparing for finals at Harvard, and drinking. Contrast that with the 145,000 person-hours and over $10 million spent by Leader Technologies. Zuckerberg’s assertion is totally illogical, yet it persists.
Obama’s and Hillary’s lies are legion. Their whoppers include: (1) Obama’s oft-repeated promise “If you like your doctor, you can keep your doctor,” (2) Obama’s claim to be a Christian to fool voters, (3) Hillary’s fabrication that a video caused the attack on the U. S. Embassy in Benghazi, and (4) Hillary’s ever-changing private email stories which are being investigated by the FBI, with new evidence proving she exposed the highest classifications of intelligence.
They have also brazenly ignored and violated laws. They encourage others to violate U.S. laws themselves, and not respect traditional authority—our borders, the U.S. Constitution and the people responsible for carrying out our laws, such as our police and military personnel. The Justice Department’s U.S. Attorneys have become little more than mobsters themselves—A fish rots from the head down.
The Deep State’s corrupt tactics in Leader v. Facebook were purposely confusing in order to discourage the public from learning the truth
The following timeline is complex. That is an Alinsky tactic: Put so many layers of lies on the onion that most people won’t take the time to peel them away.
Americans for Innovation has been peeling away the layers of this Leader v. Facebook judicial corruption onion for years. The Deep State’s onion core is now exposed. Names, places, dates, crimes and motives have been uncovered thanks to the dedicated work of many.
Soros’ New World Order wants to force its will on America and the planet. In their morality, you would be reduced to merely a consuming animal—”a useful idiot” (Alinsky). In their world, faith, hope and love are the antiquated values of weak people. They also have little need for any constitution, law or regulation that stands in their way.
* Alinsky used the phrase “a useful idiot” is sometimes attributed to Vladimir Lenin, although this is in question.
Lure users, young and old, into “The Cloud,” then ambush them
Theft of Leader Technologies’ invention of social networking was critical to the Deep State’s plan. With control of the digital essences of our lives (“The Internet of Things” aka “The Cloud”), the Deep State could achieve their new world order more quickly.